

|
|
|
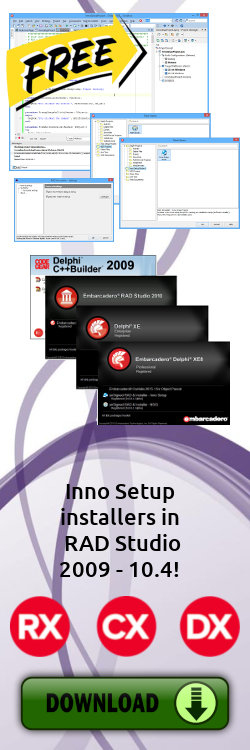
ISTool |
|
Pdanet Serial Key < HIGH-QUALITY >for digits in itertools.permutations('0123456789', 3): candidate = template.replace('???', ''.join(digits)) key = candidate.replace('?', checksum(candidate)) # Simulate a verification function (here we just print a few) if key.startswith("B4F2-7"): print(key) The script churned through thousands of possibilities in seconds, finally spitting out a single key that matched the hidden pattern the forum’s admin had left in the comments: Maya’s mind raced. In programming, loops that never end are called infinite loops . She opened a fresh terminal and typed a simple Python script that would generate every possible three‑digit combination that didn’t repeat any digit: pdanet serial key When Maya first saw the ad for pdanet —a sleek, AI‑powered network analysis tool—she imagined it would finally give her the edge she needed for her small cybersecurity consultancy. The software promised to map hidden traffic patterns, predict breach attempts, and even suggest automated patches. The only catch? A serial key, locked behind a pricey subscription. for digits in itertools Inside, she discovered a trove of features: real‑time packet visualizations, predictive threat models, and an integrated sandbox for testing patches. Within a week, Maya used pdanet to map out a sophisticated phishing campaign targeting her client’s employees. She presented a concise report, complete with actionable recommendations, and the client signed a six‑month contract on the spot. The software promised to map hidden traffic patterns, B4F2-729-9C7D Maya’s heart hammered. She copied the key, opened pdanet , and entered it. The program’s loading bar flickered, then glowed green—access granted. Word spread, and soon Maya’s consultancy was no longer a one‑person operation. She hired two more analysts, and together they built a reputation for turning cryptic clues into concrete security solutions. |
|
|||||||||||||||||

|

|
||||||||||||||||||